Secure device identity in Industrial Cybersecurity
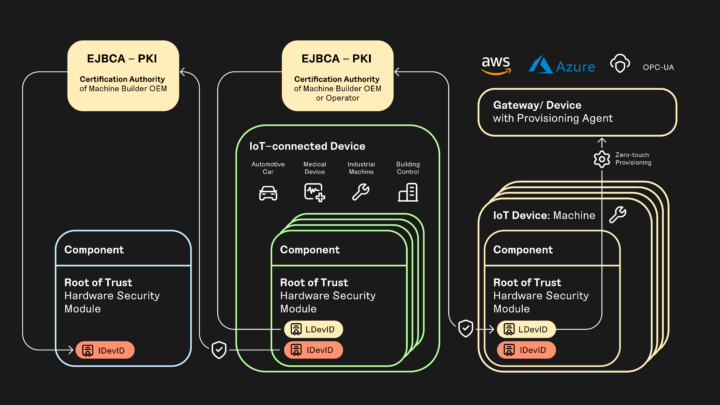
IEEE 802.1 AR provides frameworks for issuing and managing birth identities for industrial infrastructure and IoT devices. Testing and prototyping with EJBCA today will put you well on your way to building a scalable and robust supply chain security infrastructure.
Challenge
Establishing trust on the factory floor
Modern factories are made of complex assembly lines and machines themselves are built from elementary computerized bricks – Programmable Logic Controllers, Human-Machine Interfaces, sensors, Real-Time Units, and gateways. These machines interconnect with one another, with on-site and off-site systems such as Manufacturing Execution Systems (MES), Supervisory Control and Data Acquisition (SCADA), Enterprise Resource Planning (ERP), databases, digital twins, edge and cloud services, SaaS, etc. As ethernet is making more and more progress into field buses, so are IP addressing and protocols like TCP, UDP, HTTP, and MQTT to name a few. And with the latter comes the possibility for any machine or subsystem to mutually authenticate with remote peers and secure end-to-end channels by using Transport Layer Security (TLS), X.509 certificates, and private Public Key Infrastructures (PKI).
How can a factory operator enroll a new machine into their own IT and then provision connections to cloud services or SaaS with a simple process?
What can a machine builder do to ease this process?
What should the OEMs manufacturing the PLCs, HMIs, RTUs, and gateways do to make this possible?
As a developer of industrial equipment and machines or a cybersecurity expert supervising the deployment and operational security of a connected factory, implementing such technology is essential to safeguard against potential cyber threats. Modern industry standards and recommendations call for PKI and X.509 certificates to secure and authenticate communication, software, and supply chains for the industry 4.0. Examples of such standards and recommendations are:
- IEEE 802.1 AR - definition of IDevID and LDevIDs, respectively initial device certificate issued/injected by the OEM PKI and operational certificates issued and renewed by the operator PKI.
- HTTPS, MQTTS - securing HTTP and MQTT with the mutual (D)TLS protocol using X.509 certificates provisioned on both sides by their respective PKI.
- OPC-UA Part 21 (device onboarding) - A model to allow the security configuration of a device to be managed over the complete lifecycle of the Device from manufacture to decommissioning
- RFC 8995 (Bootstrapping Remote Secure Key Infrastructure – BRSKI) - Enables secure and automated provisioning of X.509 certificates to IoT devices during the bootstrapping process
Solution
Get your project off to a good start by adding the appropriate security
By levering EJBCA for your testing and prototyping today, you will be well on your way to creating a trusted supply chain based on a solution that is both scalable and robust.
Using our best practices, how-tos, and videos, you can set up a PKI to issue certificates for your industrial infrastructure and IoT devices. Once you're up, you can start tailoring your PKI and you'll have a fully functional PKI, including roles, certificate profiles, a configured use case/issuing protocol, revocation support, and system documentation.
Get started with our video tutorials and how-tos:
- Get started with Birth Identities based on IEEE 802.1AR
- Issuing of TLS certificates via EJBCA RA Web or REST
Tutorials
Get inspired
Stay up to date with the latest news and blog articles, and find out about upcoming events related to EJBCA.

#KEYMASTER: Is SCEP Still Relevant in a Post-Quantum World?

#KEYMASTER: Scaling PKI: Lessons from the Field